Pwnity is the ultimate Integrated Hacking Environment (IHE) for professional offensive operations. It unifies your entire arsenal into a single context-aware workflow with tactical reporting and visual automation.


The Integrated Hacking Environment
Master Your Arsenal. Forget the Flags.|
Pwnity is not just a tool; it's a unified wrapper for your entire arsenal. It integrates execution, parsing, and reporting into a single context-aware workflow. With smart templating, wordlist management, built-in proxying, and a native knowledge base, Pwnity eliminates the need for external bookmarks and note-taking. It handles the operational overhead so you can focus on the vulnerability.
See Pwnity in Action
From initialization to execution in 3 steps.
Modular Architecture
Detailed breakdown of the core components.
CLI Engine
COREThe force multiplier for your terminal. Unifies disparate commands into a coherent weapon system.
Target Intelligence
One command, total visibility.
Accelerate your reconnaissance by transforming raw URLs into intelligence profiles. Instantly decompose domains, map parameters, and resolve infrastructure data like IPs and SSL.
Add a target, and Pwnity populates your session with actionable context. Protocols, ports, and paths are automatically injected, ready for any tool in your arsenal.
Smart Placeholders
Dynamic Context.
Stop hardcoding flags. Use placeholders like $target.ip or $tool.silent to link your arsenal.
Change a value once, and every command updates instantly. This is Infrastructure as Code for your hacking workflow.
Smart Reporting & Curation
Quality over quantity.
Pwnity gives you an interactive extraction engine to build high-signal reports without the overhead.
Run parser apply to extract IPs, hostnames, and services from any job. You decide exactly what makes it into the final report.
Every parser is RegEx-based and 100% customizable via CLI. Add new rules or update existing ones on the fly with parser update.
Every selected finding, credential, and manual note is automatically correlated and stored in an audit-ready format.
Universal Weapon Systems
The glue between intelligence and execution.
The tool command is the heart of Pwnity. It abstracts the complexity of dozens of different tools into one unified, predictable interface.
Stop memorizing esoteric flags for 50+ tools. Once a tool is loaded, Pwnity handles the "how"—you only focus on the "what".
Everything is a variable. Inject $target.ip or $tool.commands.quick to fire complex chains without a second thought.
Your configuration is portable. Use export to turn your perfect setup into a text block for Slack or Discord, allowing your team to "aim and fire" exactly like you.
State Portability
COREYour entire engagement is just a folder.
No databases, no cloud sync, no mess.
Pwnity stores your progress as human-readable JSON files. This allows you to clone, share, or version control your session like any other code project.
Store targets, reports, and your arsenal in a simple directory. If you can move a folder, you can move your entire operation.
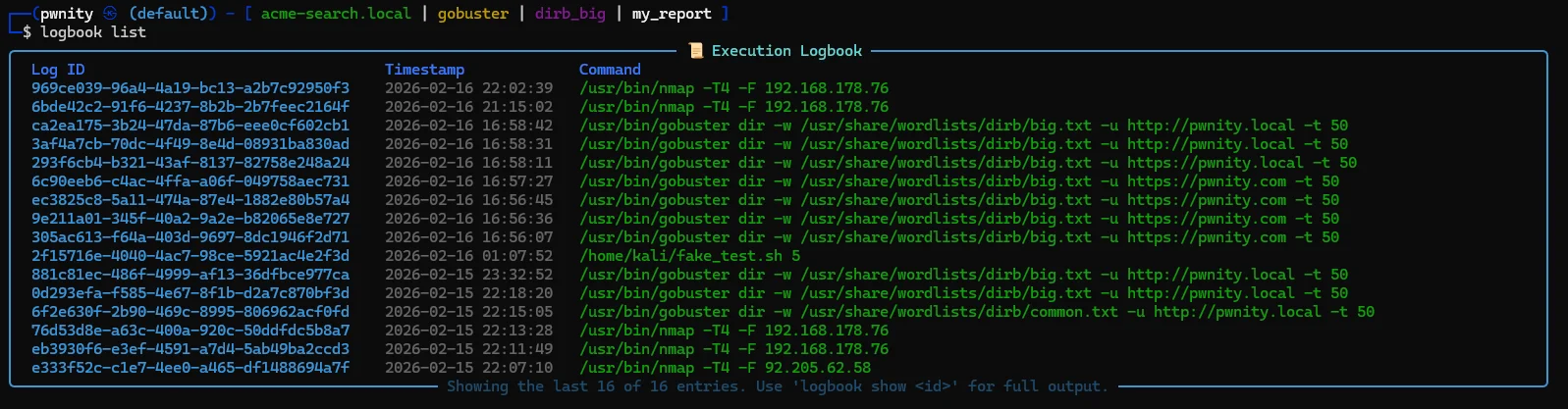
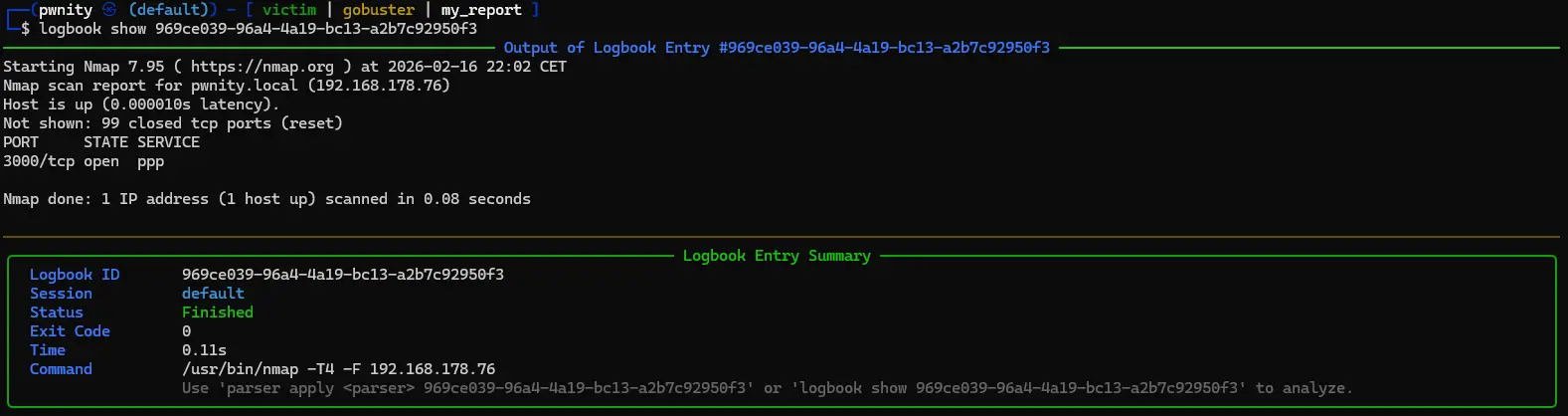
Every command is logged with forensic precision. Use logbook list to see what happened, or logbook show to retrieve the execution DNA.
Stop guessing. Every entry tracks timestamps, exit codes, and durations, making it effortless to generate evidence.
Streamlined Execution
From initialization to reporting.
Context Initialization
Define target scope, load tool configurations, and mount wordlists. All tools inherit this context automatically.
target load victim
tool load nmap
report load my_reportExecution & Parsing
Execute tools with dynamic placeholders. Pwnity handles signal trapping and output parsing into structured findings.
tool load nmap
pwn quick now
parser apply nmap <job-id>Seamless Tool Switching
Switch to a different weapon and mount a wordlist instantly. Execute complex attacks on the same target without struggling with syntax.
wordlist load dirb_common
tool load gobuster
pwn dir now
parser apply gobuster <job-id>Knowledge & Reporting
Enrich findings with notes, manage loot, and generate comprehensive markdown reports instantly.
note add "Open ports on 3000 with browsable /admin and /cfg folders"
report show
report render my_reportComplete Feature Matrix
A deep dive into the capabilities of the Integrated Hacking Environment.
UX & Productivity
- Advanced AutocompletionContext-aware suggestions for targets, tools, and nested JSON paths.
- Extensive Help SystemInteractive
manualand contextualhelpfor every flag. - Bash-Like BehaviorSubprocess execution, signal trapping, and robust command history.
- Custom AliasesCreate powerful macros and custom commands with
alias create.
Operations
- Background ExecutionLaunch complex scans with
pwn your_command bgand continue working instantly. - Multithreaded Job ManagerManage multiple concurrent tool executions without performance hits.
- On-the-fly Signal ManagementGracefully kill or interact with background jobs in real-time.
- Smart NotificationsReceive summary reports immediately when background jobs finish.
Strategic Core
- Nested Placeholder EngineDeep resolution of variables like
$target.metadata.id. - Integrated FunctionsOn-the-fly
b64encode(),urlencode(), and hashing. - Session IsolationManage multiple independent engagements without state leakage.
- Global PresetsSave complex tool configurations once and reuse them anywhere.
Data Portability
- 100% JSON StorageNo databases. Every finding, target, and log is a portable JSON file.
- Version Control ReadyAudit, share, or version-control your entire project folder with ease.
- Zero-Dependency SetupMove your environment by simply copying the data directory.
- Human-Readable ArtifactsManually edit configurations or parse findings with standard Unix tools.
Connectivity
- Multi-Protocol ProxiesIntegrated support for HTTP, SOCKS4, and SOCKS5 per session.
- Tactical HeartbeatMonitor target health and responsiveness to detect WAF blocks.
- Revshell GeneratorInstant construction for 9+ core languages and payload types.
- Custom Proxy TemplatesDefine sophisticated proxy chains and re-use them across sessions.
Strategic Assets
- 19+ Predefined Tool WrappersOut-of-the-box support for Nmap, Gobuster, Nikto, and more.
- 16+ Tactical WordlistsOptimized lists for common fuzzing and brute-force scenarios.
- 14+ Knowledge Library EntriesQuick-access links to HackTricks, PayloadsAllTheThings, and documentation.
- 6+ High-Signal ParsersRegEx engines to extract actionable intelligence from tool output.
Technical Showcase
A high-fidelity deep-dive into the Pwnity operational interface.
Get Started in Seconds
No databases, no complex setup. Just clone and pwn.
100% Local & Private
Your data never leaves your machine. No databases to configure, just portable JSON files.
Context Aware
Pwnity remembers your target and tools. Stop juggling IPs and focus on the vulnerability.
Wrapper Ready
Wraps Nmap, Gobuster, and more out of the box. Easily extendable with custom JSON templates.
Roadmap
Building the ultimate hacking workbench, one commit at a time.
Pre-Beta (Stable)
- Core CLI Framework
- Session-Based Context Management
- Tool, Target & Wordlist Library
- Placeholder & Job System
- Predefined Tool Presets
- Initial Documentation & Guides
In Development
- Web UI (Pro)
- Visual Node Editor
- Advanced Reporting Formats
Planned
- Official Kali Linux Package
- Community Hub for Sharing
- AI Command Suggestions